Top 10 API Gateway Use Cases in System Design
As your system evolves from a monolith to microservices, a pattern quickly emerges: every service starts rebuilding the same things.
Authentication. Rate limiting. Request logging. The same logic gets duplicated across services, with slight variations and inevitable bugs.
An API Gateway fixes this by introducing a single entry point for all client requests.
Instead of spreading these cross-cutting concerns across your services, you move them to one place. The gateway handles routing, security, traffic control, and more, so your services can stay focused on business logic.
In this article, we’ll break down the top 10 API Gateway use cases, how they work, and why they should belong at the gateway layer.
1. Request Routing
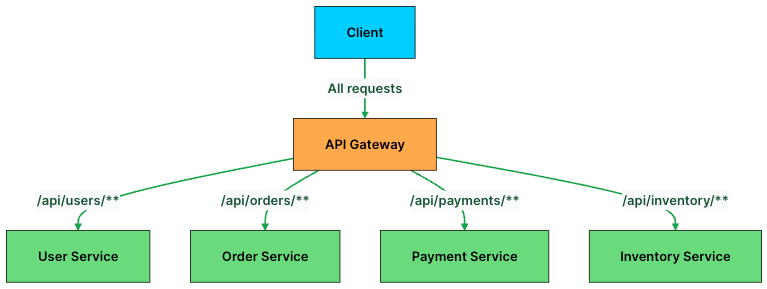
At its core, an API Gateway is a traffic controller. Its primary job is simple: take an incoming request and send it to the right service.
In a microservices architecture, each service owns a specific domain such as users, orders, payments, or inventory. But clients don’t need to know where these services live or how many instances are running. They just send requests to the gateway, and the gateway takes care of the rest.
Routing decisions are usually based on things like the URL path, HTTP method, headers, or query parameters. For example, requests to /api/users go to the User Service, while /api/orders is handled by the Order Service.
Here’s what a routing configuration looks like in practice:
# API Gateway routing rules
routes:
- path: /api/users/**
service: user-service
methods: [GET, POST, PUT, DELETE]
- path: /api/orders/**
service: order-service
methods: [GET, POST]
- path: /api/payments/**
service: payment-service
methods: [POST]
- path: /api/inventory/**
service: inventory-service
methods: [GET]Behind the scenes, the gateway often integrates with service discovery systems like Consul or Kubernetes DNS. So when a new instance of a service spins up, the gateway can find it automatically without any manual updates.
This decouples clients from your backend. Services can scale, move, or even be renamed without breaking anything on the client side.
But routing alone isn’t enough. Once a request reaches your system, you still need to decide whether the client should be allowed to make that request in the first place.
2. Authentication and Authorization
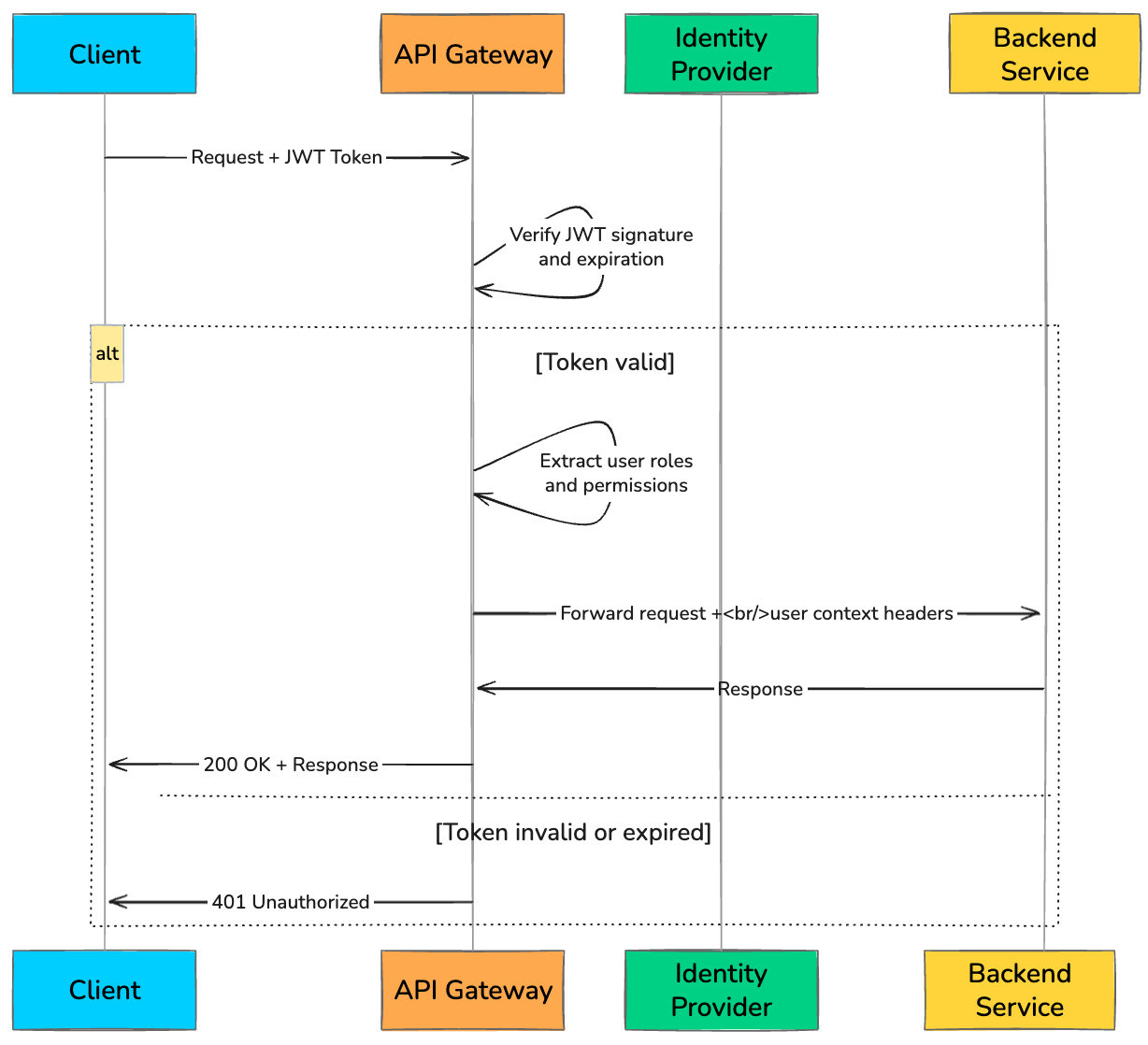
Every API request needs to answer two questions: Who is this? And are they allowed to do this?
Without an API Gateway, each microservice has to implement its own authentication and authorization logic. That quickly leads to duplicated code, inconsistent checks, and subtle security gaps.
An API Gateway fixes this by making security a first-class, centralized concern. It intercepts every request, validates the credentials, and only forwards requests that pass the checks. By the time a request reaches a backend service, it’s already trusted.
The most common approach is validating a JWT (JSON Web Token). The client sends the token in the Authorization header, and the gateway verifies its signature, expiration, and permissions before routing the request.
A typical token validation flow at the gateway looks like this:
def authenticate_request(request):
token = request.headers.get("Authorization", "").replace("Bearer ", "")
if not token:
return {"status": 401, "error": "Missing token"}
try:
# Verify JWT signature and decode claims
payload = jwt.decode(token, PUBLIC_KEY, algorithms=["RS256"])
# Check token expiration
if payload["exp"] < current_time():
return {"status": 401, "error": "Token expired"}
# Check if user has required role for this endpoint
required_role = get_required_role(request.path, request.method)
if required_role not in payload.get("roles", []):
return {"status": 403, "error": "Insufficient permissions"}
# Attach user context for downstream services
request.headers["X-User-ID"] = payload["sub"]
request.headers["X-User-Roles"] = ",".join(payload["roles"])
return {"status": 200, "user": payload}
except jwt.InvalidTokenError:
return {"status": 401, "error": "Invalid token"}Gateways can also support API keys for internal services and OAuth 2.0 flows for third-party integrations. The key idea is simple: enforce security once, at the edge, instead of reimplementing it everywhere.
Once you know who the client is and what they can do, the next challenge is controlling how much they can do without overwhelming your system.